Loading...
Searching...
No Matches
capabilities.c File Reference
(/usr/bin/git 2025-06-05, commit: 45a2f9b7)
Implementation of functions related to process capability handling. More...
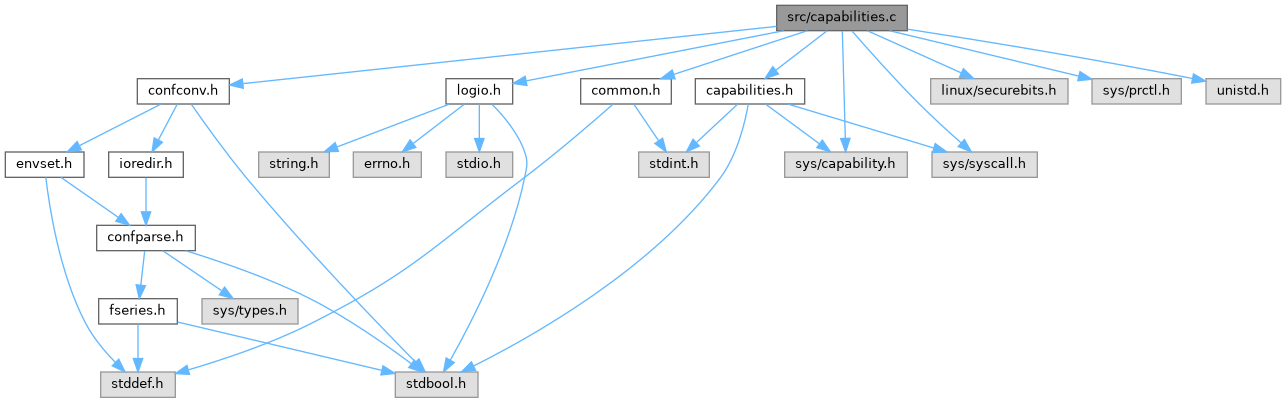
#include "capabilities.h"#include <linux/securebits.h>#include <sys/capability.h>#include <sys/prctl.h>#include <sys/syscall.h>#include <unistd.h>#include "common.h"#include "confconv.h"#include "logio.h"
Include dependency graph for capabilities.c:
Functions | |
| static int | crinitProcCapGet (cap_user_data_t out, pid_t pid) |
| int | crinitCapConvertToBitmask (uint64_t *bitmask, const char *capabilities) |
| int | crinitCapGetInheritable (pid_t pid, uint64_t *result) |
| bool | crinitCapIsCapsetEffective (cap_value_t cap, pid_t pid) |
| int | crinitCapSetAmbient (uint64_t capMask) |
| static int | crinitSetCapStateInheritable (uint64_t capMask, cap_t capState) |
| int | crinitCapSetInheritable (uint64_t capMask) |
| int | crinitCapRetainPermitted () |
Detailed Description
Implementation of functions related to process capability handling.
Function Documentation
◆ crinitCapConvertToBitmask()
| int crinitCapConvertToBitmask | ( | uint64_t * | bitmask, |
| const char * | capabilities | ||
| ) |
Convert capability names to integral value and set it in bitmask.
- Parameters
-
bitmask Bitmask to maintain capability settings. capabilities Array of capability names
- Returns
- 0 if each capability could be converted and set in the bitmask, -1 otherwise.
◆ crinitCapGetInheritable()
| int crinitCapGetInheritable | ( | pid_t | pid, |
| uint64_t * | result | ||
| ) |
Get a process' inheritable capability set
- Parameters
-
pid The ID of the process whose capabilities are retrieved. result Pointer to result bitmask that holds the inheritable capability set.
- Returns
- 0 on success, -1 on error
◆ crinitCapIsCapsetEffective()
| bool crinitCapIsCapsetEffective | ( | cap_value_t | cap, |
| pid_t | pid | ||
| ) |
Test if a capability is set in a process' effective capability set.
- Parameters
-
cap The capability to test. pid The ID of the process whose capabilities are checked.
- Returns
- true if capability is set, false else
◆ crinitCapRetainPermitted()
| int crinitCapRetainPermitted | ( | ) |
Configure a process to retain its permitted set of capabilities.
- Returns
- 0 on success, -1 on error
◆ crinitCapSetAmbient()
| int crinitCapSetAmbient | ( | uint64_t | capMask | ) |
Set a process' ambient capability set
- Parameters
-
capMask The capability set encoded as a bitmask
- Returns
- 0 on success, -1 on error
◆ crinitCapSetInheritable()
| int crinitCapSetInheritable | ( | uint64_t | capMask | ) |
Set a process' inheritable capability set
- Parameters
-
capMask The capability set encoded as a bitmask
- Returns
- 0 on success, -1 on error
◆ crinitProcCapGet()
|
static |
Gets capabilities of process specified by PID.
- Parameters
-
out Return pointer for capabilities. Note, that the Linux API defines cap_user_data_t as a pointer to struct __user_cap_header_struct. The given pointer needs to point to at least two elements. pid PID of the process from which to get the capabilities.
- Returns
- 0 on success, -1 on error
◆ crinitSetCapStateInheritable()
|
static |